Password Safety Series: Bonus Material
In the first post in this series, we mentioned that password recovery systems (like answering security questions in order to reset a password) were a potential vector of attack. As we wrap up our password safety series, let’s look at how to thwart this attack and an interesting resource around hacked passwords.


Lie on Your Security Questions
Some password recovery systems only require the answers to a couple of questions (no additional hurdles like clicking a link sent to the email address on file). If you can remember the answers to those security questions, so might someone else. Think about it. If someone knew you well, had accessed to your social media profiles, or could research public information about you, would they be able to answer your security questions? Things like maiden name, favorite shows, first car or pet’s name aren’t hard to find.
To avoid having someone guess the correct answers, you should lie on these questions. If you’re worried about remembering the lies, use the same lie every time but mix in some part of the question.
Consider these examples:
What was the make and model of your first car?
CHEESE CAR
What is your favorite TV show?
CHEESE SHOW
What is your maiden name?
CHEESE NAME
Now you can thwart would-be impersonators of you who may try to manipulate these password recovery systems.
Is Your Password Already Known?
A security researcher named Troy Hunt runs the website haveibeenpwned.com, which lists publicly dumped data from past data breaches and describes the information stolen in each breach. If you sign up (free for personal use), you’ll get a notification anytime your email appears in a data breach of a sensitive nature. In recent years, Troy has also added dumped passwords to his database.
https://haveibeenpwned.com/Passwords
Why? To help people avoid using passwords that have been previously compromised. These compromised passwords are often used by hackers to try to gain access to other online accounts, a technique known as credential stuffing.
As an individual, you can use the search feature to look up old passwords or passwords you are considering to see if it’s already been seen in a data breach previously. For fun, look up how many times the password “1qaz2wsx” has been seen. You’ll quickly scratch it off your list of password choices!
Use All Your Tools and Strategies
The goal is strong protection for our online accounts. There are several tools and strategies to help us achieve this goal. One is using a password recipe to build a strong password – one that is not in Troy Hunt’s password database! We showed you a password recipe last week, but you can never have too many recipe ideas, right?
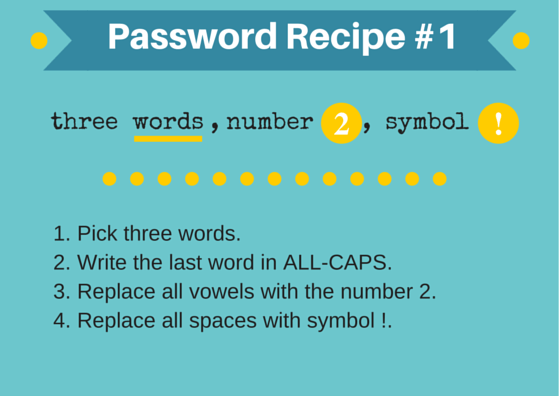
Let’s follow it.
- endless summer fun
- endless summer FUN
- 2ndl2ss s2mm2r F2N
- 2ndl2ss!s2mm2r!F2N
This recipe can be used with any phrase to create a password that won’t be easily cracked.
Hackers will use multiple angles to hack your accounts, so pull out all the tools in your toolkit: strong passwords, phishing recognition techniques, lies on password recovery questions, two factor authentication, and password managers.